On March 31, 2026, the popular HTTP client was hijacked, branded as the NPM Axios supply chain attack, to deliver a cross-platform Remote Access Trojan, targeting over 100 million weekly downloads. Attributed to UNC1069, the attack used stolen credentials and a “phantom dependency” to plant malicious code in package.json, bypassing OIDC protections.
Axios is one of the most widely used JavaScript HTTP‑client libraries, with well over 100 million weekly downloads on npm. Understanding this Axios NPM supply‑chain attack helps developers, security teams, and platform operators see how relatively this issue can compromise systems.
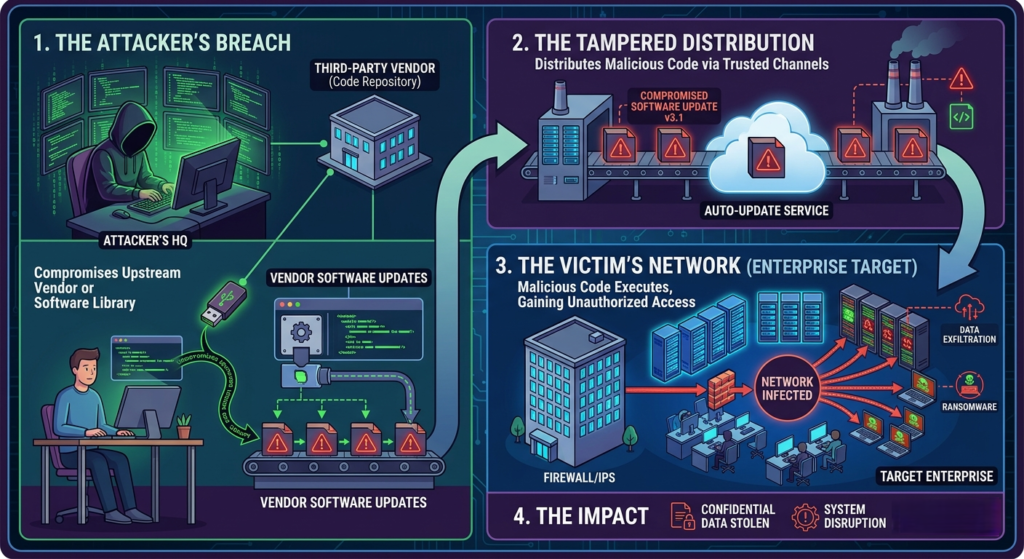
What is a supply‑chain attack on npm?
A supply‑chain attack in the npm ecosystem occurs when an attacker hijacks a trusted package (or its dependencies) so that anyone who installs Node.js npm or updates it automatically pulls in malicious behavior. Instead of targeting each victim individually, the attacker hijacks a single node in the dependency graph, such as a popular library like Axios, and lets automated tools like npm install or CI/CD pipelines spread the payload.
Common patterns in npm supply‑chain attacks include:
- Trojaned packages: The library’s source or build process is modified to run harmful code.
- Malicious dependencies: A dependency is added to the package.json and then abused via install scripts.
- Phantom dependencies: The attacker adds a package that exists only for the side effects of its preinstall or postinstall scripts, not for any real functionality.
Axios fell victim to the “malicious dependency” and “phantom dependency” variants, where the attacker compromised a maintainer account to publish vulnerable versions that pulled in an under payload via a third‑party package.
How the Axios NPM attack was discovered
Public analyses of the Axios incident describe a tight, operationally disciplined attack window of roughly three hours during which the malicious versions were live on the npm registry. Attackers exploited access to the npm account of a key Axios maintainer, enabling them to publish new releases that appeared completely legitimate to automated tools and to most users.
The two compromised versions were:
axios@1.14.1(main branch).axios@0.30.4(legacy branch).
This dual‑branch targeting maximized exposure across projects that were still pinned to older Axios versions, amplifying the potential impact without requiring victims to manually upgrade. Within minutes of publication, automated npm security scanners flagged suspicious behavior, and npm administrators removed the compromised packages, limiting the attack window.
Key technical steps in the attack flow
Rather than directly embedding a large malicious payload inside Axios itself, the attackers used a technique known as a phantom‑dependency attack. In both Axios releases, the attackers added a new dependency named plain‑crypto‑js@4.2.1 to the package.json manifest.
- The plain‑crypto‑js package contained a postinstall script that ran automatically every time someone ran npm install in an affected project. During this phase, the script reached out to an attacker‑controlled domain.
- The postinstall script fetched a heavily obfuscated JavaScript file, often referred to as setup.js. This file contained logic to detect the victim’s operating system (Windows, Linux, macOS) and download a platform‑specific binary payload from the same C2 infrastructure.
- The delivered payload behaved as a Remote Access Trojan (RAT) with cross‑platform capabilities. Once installed, it could perform local system reconnaissance and obtain credentials, clipboard contents, and other sensitive data. Accept remote commands and exfiltrate collected information back to the attacker’s command‑and‑control (C2) servers.
Stay Ahead of Modern Cyber Threats!
The NPM Axios vulnerability highlights how trusted packages can be compromised to spread malicious code. Secure your application now!
Why Axios was such a high‑value target
Axios is a fundamental HTTP‑client library adopted by millions of JavaScript and Node.js projects, including frameworks, web applications, and internal tooling. Its high download volume and widespread inclusion in CI/CD pipelines made it a prime candidate for supply‑chain exploitation.
Dependency chains
Many projects depend on Axios transitively, meaning they don’t list it directly but still receive it via other packages. This increases the number of potential victims far beyond those who explicitly list Axios in their package.json
Automated installs in CI/CD
Continuous Integration and Continuous Delivery pipelines routinely run npm install as part of their workflows. If those pipelines were active during the 2–3 hour window when the malicious Axios versions were live, the postinstall scripts would execute automatically, often with elevated privileges.
Developers Data exposure
When developers run npm install locally, the same install scripts execute on their machines. A compromised developer laptop can provide attackers with access to repositories, credentials, and internal tools, making Axios‑based postinstall attacks a gateway to much broader breaches.
Get 20% off on your first hosting purchase. Provide everything you need to create your website.
How to Secure from this specific Axios incident
For organizations that may have pulled in the malicious Axios versions during the brief window, remediation and detection steps are critical.
- Scan all projects for axios@1.14.1 and axios@0.30.4 and flag any usage.
- Look for plain‑crypto‑js@4.2.1 in lockfiles (package‑lock.json, yarn.lock) or logs of
npm installjobs. - Check the network traffic and DNS domains related to the C2 infrastructure. Block malicious domains at DNS / firewall.
- Replace 1.14.1 and 0.30.4 with the latest patched Axios releases and verify that plain‑crypto‑js is no longer present as a dependency.
- Force a fresh
npm installornpm ciin pipelines after removing the malicious versions to ensure no backdoor packages remain. - Assume that any credentials or cloud tokens stored on affected machines may have been exfiltrated. Rotate credentials and tokens.
Security Recommendations
The npm vulnerability illustrates several systemic weaknesses in how modern JavaScript ecosystems handle dependencies and automation.
- Pin major and minor versions of critical libraries to avoid suddenly receiving an unexpected bad release.
- Prefer
npm ciin CI/CD, which ignorespackage.jsonand rebuilds strictly frompackage‑lock.json, reducing the chance of last‑minute dependency injection. - Where security policy allows, consider running
npm ci --ignore‑scriptsin non‑development environments to prevent automatic execution of postinstall code. - Enforce MFA for all npm GitHub accounts, especially those controlling high‑impact packages.
Summary
The Axios npm supply‑chain attack was a case of how a single maintainer‑account compromise can turn a widely trusted open‑source library into a malware‑delivery vector. By injecting a phantom dependency with a malicious postinstall script, attackers delivered a cross‑platform RAT that infected thousands of systems in a matter of hours. The incident underscores the need for stricter dependency pinning, attention to install‑script execution, and robust registry‑level controls, so that the next npm package remains a productivity tool, not an entry point for long‑term attacker access.
If you found this guide helpful, check out our other guide on installing Git on Windows, which offers a practical explanation to help you better understand the version control system.
FAQ
What is the NPM Axios supply chain attack?
It’s a security incident where the Axios package or its dependencies are compromised to deliver malicious code to developers.
How does a supply chain attack work in NPM?
Attackers inject malicious code into trusted packages, which then spreads to all projects using those dependencies.
Why is Axios a target for attackers?
Axios is widely used, so compromising it can impact a large number of applications and developers globally.
How can developers protect against such attacks?
By auditing dependencies, using lock files, enabling 2FA, and monitoring for suspicious package updates.
What impact can this attack have on applications?
It can lead to data theft, unauthorized access, or execution of harmful code within affected systems.